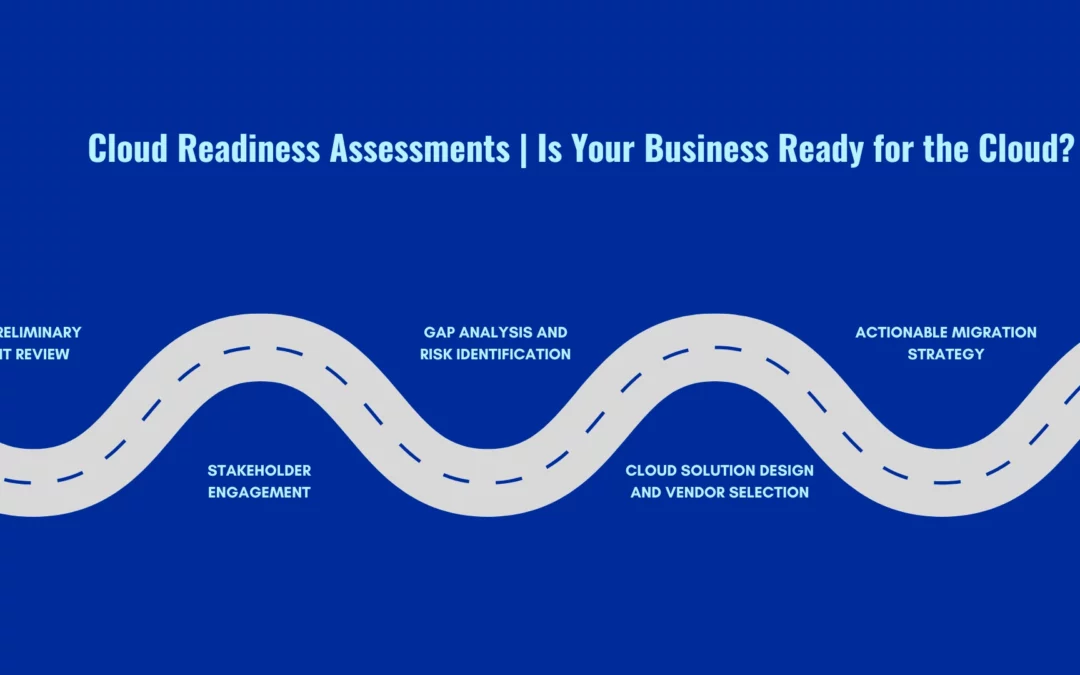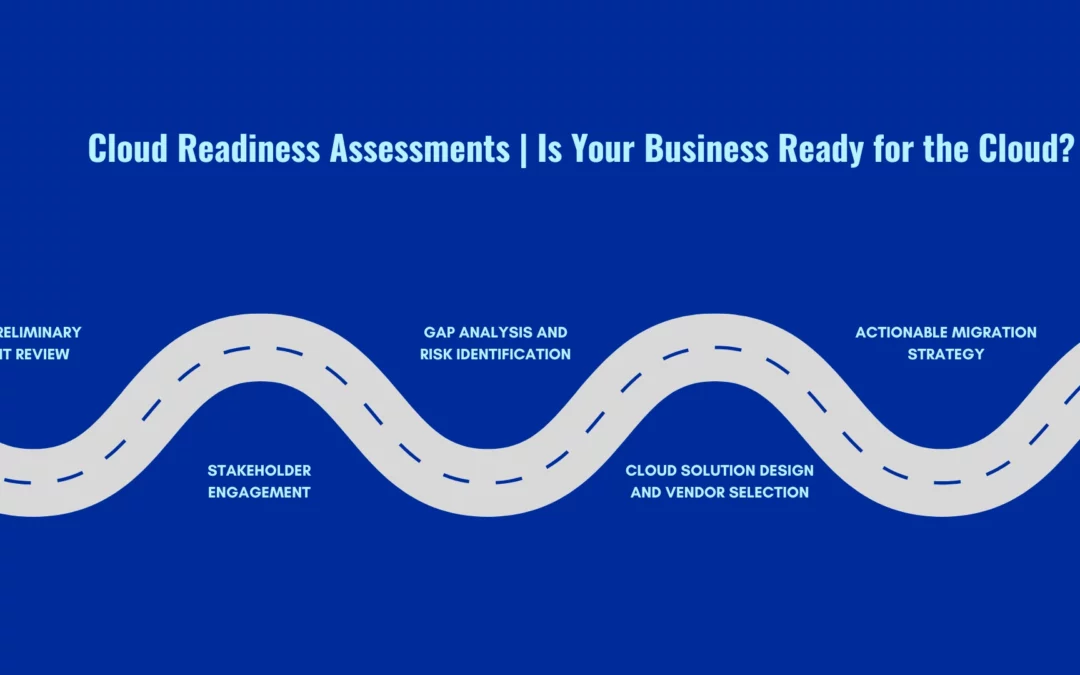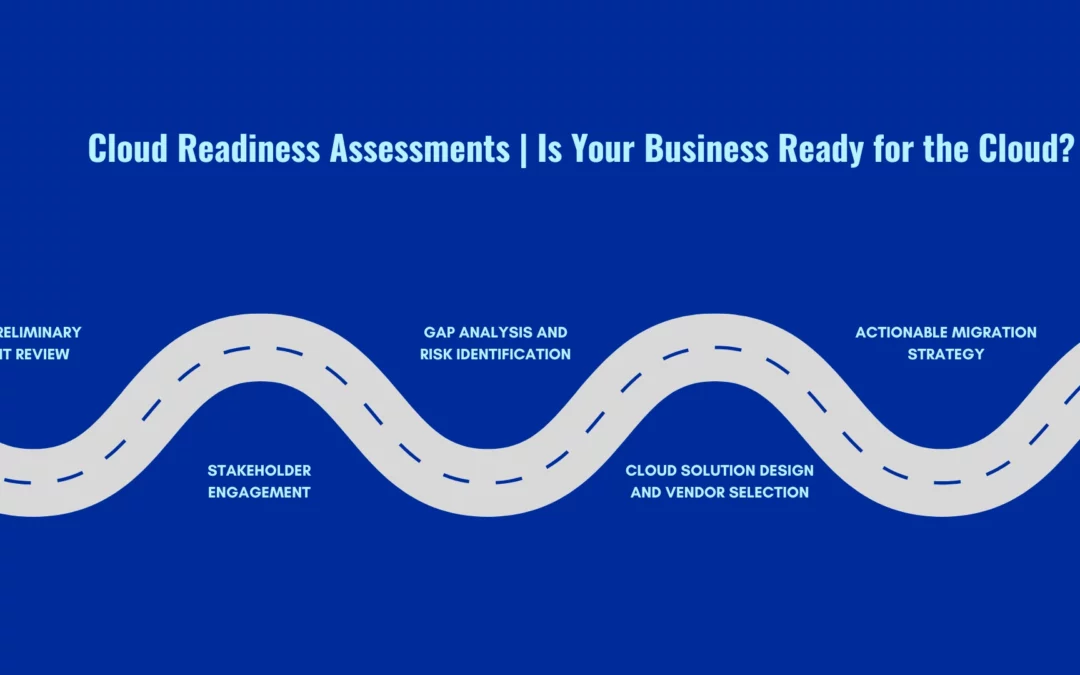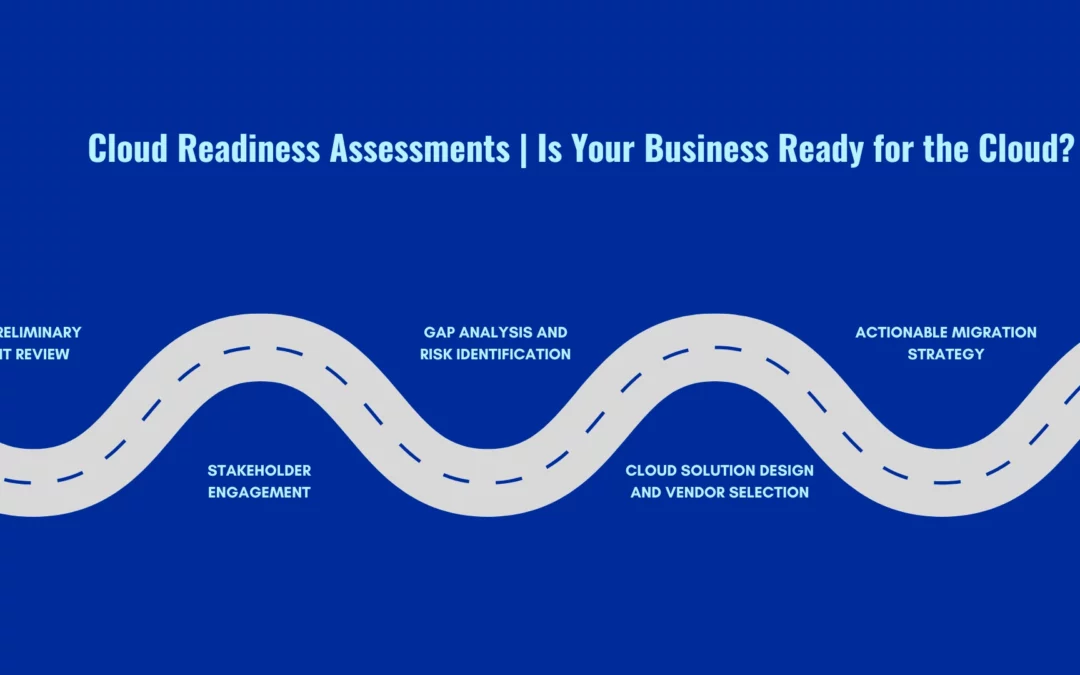
by Nikhath K | Oct 6, 2025 | Cloud-Native Application, Latest
Discover how a cloud readiness assessment helps organizations evaluate infrastructure, applications, security, and processes to ensure a smooth cloud transition. Get a comprehensive checklist from our Cloud Management Support Team to guide your organization through a...
by Manu Menon | Oct 14, 2024 | Azure, DevOps, Latest
Github Advanced Security For Azure DevOps GitHub Advanced Security for Azure DevOps (GHAS for Azure DevOps) is a comprehensive set of security tools embedded within the Azure DevOps workflow. Its primary goal is to strengthen the security of code repositories while...
by Manu Menon | Sep 19, 2024 | Latest, Software Development
Importance Of API Security Best Practices It is extremely important to learn about the API security best practices. An API (Application Programming Interface) serves as a communication bridge between two or more software programs or components, providing a set of...
by Manu Menon | Sep 12, 2024 | Latest, Software Development
What is the Secure Software Development Life Cycle (SSDLC)? Agile software development and DevOps are two separate but complementary approaches in the software The Secure Software Development Life Cycle (SSDLC) is a methodical approach to software development that...
by Manu Menon | Jun 18, 2024 | Latest, Vulnerability Scanning
Vulnerability Scan vs Penetration Test: What is the Difference? It is important to learn more about vulnerability scan vs penetration tests. These are the two distinct methods employed in cybersecurity to evaluate and bolster an organization’s security...