Secure remote technical support – ISO 27001:2022 certified
When it comes to the security of your customer and server data, we leave nothing to chance.
Home »
We understand the amount of trust you place on us when you give access to your and your customers’ intellectual property such as website data, payment data, server logins, etc. This is why we became the first and only company in the web hosting industry to implement the strictest security standard for secure remote technical support – ISO 27001. With ISO 27001 certification, we are light years ahead of even SAS 70 audited companies who claim high security in their operations.
How information security is assured at Bobcares
- Any information that originates from your company is received through identified channels (email, phone, chat, etc.), and are stored or displayed in pre-defined systems (central database, work stations, etc.). All these channels and systems are exhaustively identified, and noted as information assets.
- Data originating from your company is given a minimum classification level of “Confidential”, and security systems are implemented so that only the team members currently assigned to you will be able to see it.
- The security system enforces multiple levels of authentication and authorization to ensure that only engineers with currently valid access can get into your servers (terminal access, administrator access, etc.) or access client information (help desk system, billing system, etc.).
- Each engineer is trained to follow a strict code of secure practices (password policy, identifying intellectual property, etc.) as mandated by ISO 27001, and security systems enforce these policies in various interfaces.
- An internal security team headed by the Information Security Manager continuously audits the reliability of these processes and systems, and make improvements as needed.
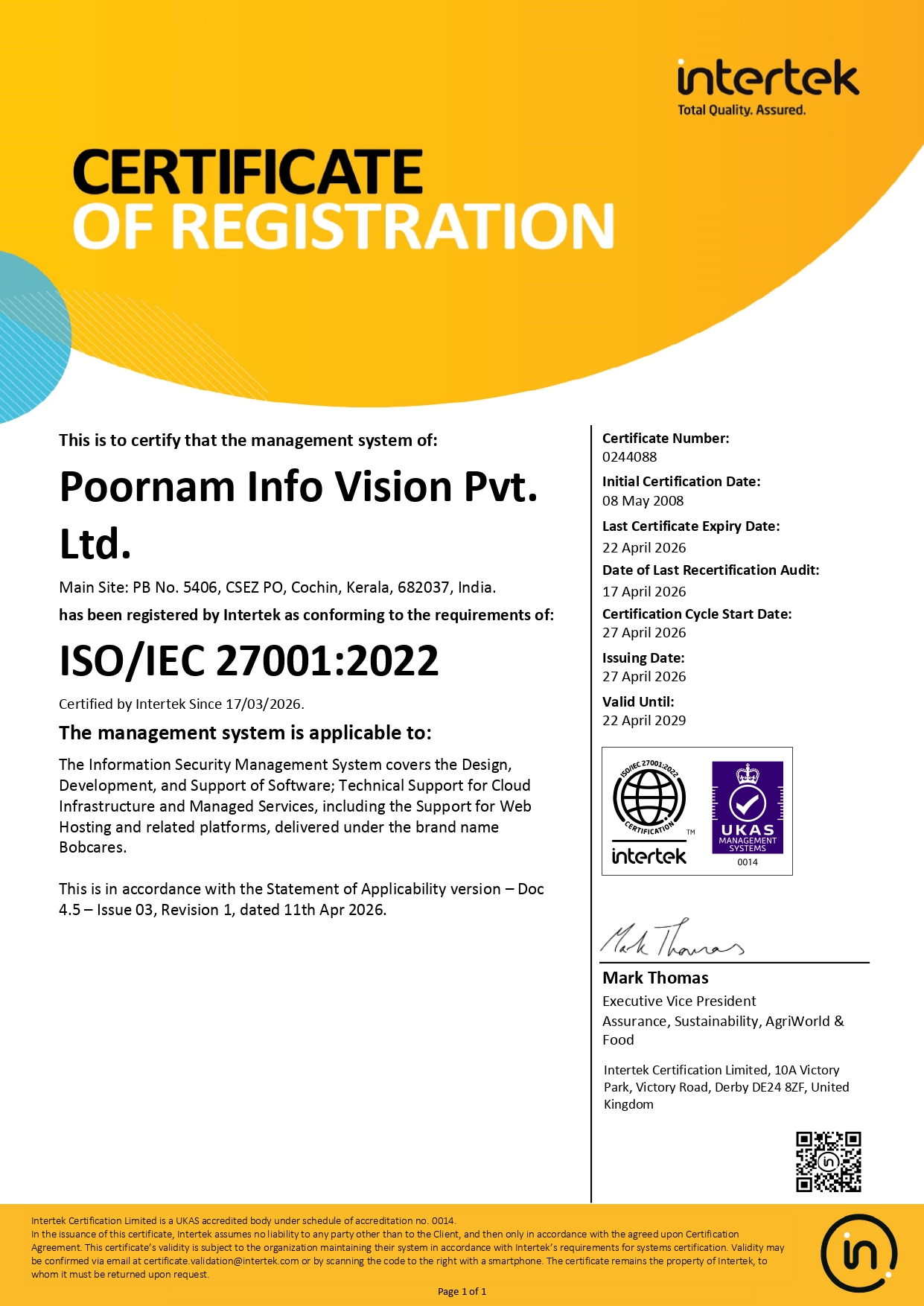
- An external UKAS accredited agency (Intertek) audits the security systems annually to verify adherence to the international standard. Upon successful audit completion, ISO 27001:2022 certificate is granted to Poornam Info Vision Pvt. Ltd. (parent company of Bobcares) for one year.
How ISO 27001 helps your business
- Your business identity, server login details and customer details are accessible only to authorized individuals. All details originating from your company is stored in encrypted media, and protected with multiple levels of authentication.
- You get engineers who are trained to think and operate with security as a priority. They wouldn’t make mistakes such as choosing a weak password, leaving open a temporary access port, etc.
- Your operations are secured by a well thought out international standard which leaves nothing to chance. Every part of the support process is secured by two or more levels of cross verification.