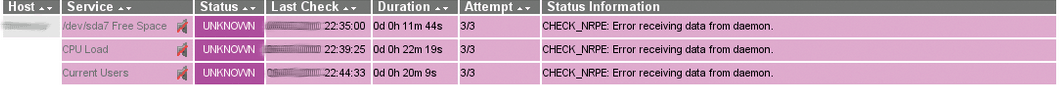
Are you receiving ‘check_nrpe: error receiving data from daemon’ in Nagios?
The reasons for this error are the bad configuration of NRPE, insecure connection with the remote server, etc.
At Bobcares, we monitor remote servers using Nagios, as part of our Server Management Services.
Today, let’s see how our Support Engineers fix this Nagios error.
How does Nagios monitor a remote machine?
Using Nagios is one of the preferred ways to monitor remote machines. Because it has flexible and configurable features.
The Nagios uses an add-on for monitoring a remote server, namely, Nagios Remote Plugin Executor aka NRPE. This add-on enables the execution of scripts to monitor remote machines.
The NRPE add-on has two parts, check_nrpe plugin in the Nagios server and NRPE daemon at the remote server.
Let’s see how it monitors.
- Initially, the Nagios server executes the check_nrpe plugin. This gives information to the remote server about the services to be checked.
- It contacts the NRPE daemon using an SSL connection.
- The NRPE daemon runs appropriate plugins to checks the services.
- The result is sent back to the check_nrpe plugin.
- Finally, the Nagios server displays the results.
Next, let’s see why does Nagios monitoring fails.
Why does Nagios fail to receive data from daemon?
When the check_nrpe plugin doesn’t receive data from the NRPE daemon, the Nagios servers shows the error,
A few reasons for this error are,
- Incorrectly compiled check_nrpe on the Nagios host.
- Using the no SSL switch (-n) with check_nrpe.
- Incorrect ownership and file permissions on the remote host.
- Firewall restrictions.
Let’s see how our Support Engineers fix this error.
How we fix check_nrpe error receiving data from daemon?
Now let’s see how we fix this error in different situations.
No SSL switch to connect with the remote host
Sometimes users add -n switch to the command definitions in the NRPE configuration file. This can end up in error if the remote host was compiled to connect with SSL.
We use the -n option only for test purposes if the SSL is not enabled on the remote end. In all other situations, we compile SSL in both machines. And we do not recommend the usage of -n switch in check commands.
Improper configuration
In some cases, improper configuration of /etc/nagios/nrpe.cfg file also can cause this error. Some major mistakes we often see are:
- Usage of white spaces in allowed_hosts. There should not be any white space in it.
- Similarly, the hosts must be separated by coma only.
We correct such errors in the config file.
Incorrect file permissions and ownership
Similarly, the permissions and ownership of Nagios files in the remote host also matter. The nagios user should have enough permissions on the related files and folders.
Hence we change ownership of folders in /usr/local/nagios using:
chown -R nagios:nagios /usr/local/nagios/*
Additionally, the files must be readable by the Nagios user.
Firewall restrictions
If the firewall of the remote server is blocking the port used by Nagios, the same error can show up. So we also check the firewall rules in the server.
We always ensure to allow 5666 port in the server.
[Having trouble in monitoring your servers? – Our Experts are available 24/7.]
Conclusion
In short, check_nrpe error receiving data from daemon occurs mainly due to incorrectly compiled NRPE on the remote host. Today, we saw how our Support Engineers fixed this error.





