In our previous post, we saw how to secure your OpenSSL servers from SWEET32 Birthday Attack. But OpenSSL isn’t the only server that’s affected by this bug.
Use of block cipher encryption algorithm makes OpenVPN servers also vulnerable to this attack. The OpenVPN vulnerability is tracked with the CVE number CVE-2016-6329.
Read: SWEET32 Birthday attack : How to fix TLS vulnerability (CVE-2016-2183)
Today we’ll see how OpenVPN is affected by SWEET32 bug and how to protect your servers.
What is OpenVPN SWEET32 vulnerability?
In OpenVPN tunneling, the encryption algorithms used are: DES, 3DES, AES and Blowfish. The default algorithm in OpenVPN is the bf128 (Blowfish with 128-bit key).
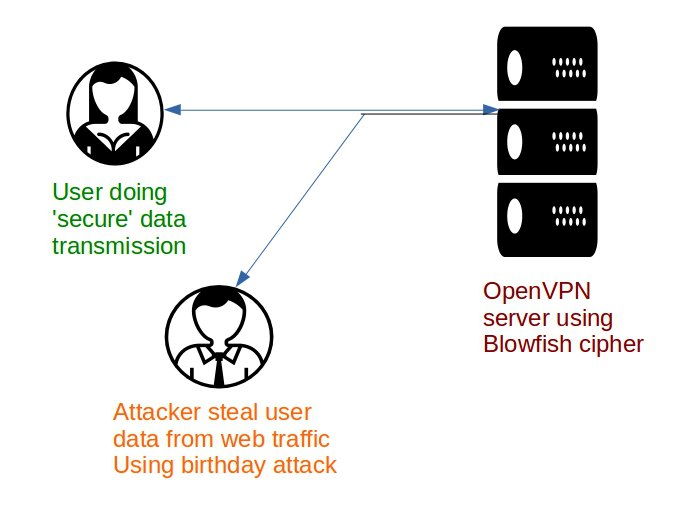
The use of short 64-bit block cipher such as Blowfish has made OpenVPN vulnerable to the SWEET32 birthday attack, the new exploit released on 24th August 2016.
OpenVPN connections secured with long-lived Blowfish algorithm can be decrypted using this SWEET32 birthday attack.
In this, attackers can recover secure HTTP cookies by sniffing around 705 GB of traffic. Attackers can thus gain access to your confidential information such as credit card details.
SWEET32 Birthday attack on OpenVPN vulnerability
Are you vulnerable to SWEET32 OpenVPN bug?
If you are running OpenVPN versions lower than 2.3.12, where the default algorithm is Blowfish, then you are vulnerable to this bug.
To know the list of cipher algorithms supported by your OpenVPN server, use the command:
openvpn --show-ciphers
How to fix SWEET32 vulnerability in OpenVPN
OpenVPN team released their latest version OpenVPN 2.3.12, that will discourage the use of 64-bit ciphers. So the best solution is to download and install this latest secure version.
You can download the latest version from the OpenVPN site and extract it and install it in your server using these steps:
tar xfz openvpn-[version].tar.gz cd .. ./configure make make install
The new version supports the more secure AES ciphers, and hence its not vulnerable to SWEET32 exploit.
How to mitigate SWEET32 vulnerability in OpenVPN
In cases where an immediate upgrade of the OpenVPN service is not feasible, there is a work around to mitigate the attack.
The safest workaround for OpenVPN users is to change the cipher algorithm from the default Blowfish to AES.
Using a strong cipher such as ‘
AES-256-CBC'To use an AES algorithm with 256 bits encryption, add this line to both client (client.conf) and server config (server.conf) files of OpenVPN:
cipher AES-256-CBC
It is also possible to update the Cipher from the OpenVPN management console.
A strong OpenVPN configuration file would look like:
client
dev tun
proto udp
remote in.privateinternetaccess.com 1197
resolv-retry infinite
nobind
persist-key
persist-tun
cipher aes-256-cbc
auth sha256
tls-client
remote-cert-tls server
auth-user-pass
comp-lzo
verb 1
reneg-sec 0
crl-verify crl.rsa.4096.pem
ca ca.rsa.4096.crt
disable-occ
In short
Today we saw how to secure your OpenVPN servers from the SWEET32 birthday attacks due to OpenVPN vulnerability, by upgrading the server and securing the ciphers.
At Bobcares, we also enable other security features in OpenVPN, such as using TLS authentication secret, using 2048-bit RSA keys for all certificates, setting TLS v1.2 as minimum version, etc.
As with the case of default cipher, the default message authentication for OpenVPN – SHA-1, is also weak. So we use a strong authentication, SHA-256 in our servers for security.
Our routine maintenance tasks and security audits helps us to ensure that the OpenVPN servers we maintain for our customers are secure and not prone to any attacks.





