Spam mails are more than a mere nuisance for web hosts. When a server is spammed, valid mails get lost or delayed indefinitely in the pool of spam mails.
Equally panicky situation is outbound spamming from your server. Your mail server IP can easily get blacklisted, causing email delivery failures for your customers.
How we block inbound spam in cPanel servers
Our Server Support Specialists help hundreds of web hosts, digital marketers and website owners keep their servers spam free.
Here, we’ll give a sneak-peak into what we do to prevent inbound spamming in cPanel servers.
1. Spam filters to filter out incoming spam
In cPanel servers, the most commonly installed Spam filters are ‘Spamassassin’ and Mailscanner. But simply installing SpamAssassin will not be sufficient to prevent spamming in servers.
The default rule-set of SpamAssassin is configured for generic spam and may not filter all types of spam that hits your mail server. To ensure that no spam gets into your server, we configure custom rules to examine incoming mails and filters to block spam.
Bobcares engineers also use extended email logging and email header inspection to identify the spam mails that escape the default rule-set and reach the mailboxes. We then configure custom spam filter rules to block those spam mails.
Another security feature we implement in mail servers, is the scanning of incoming mails for malicious attachments and viruses, using antivirus software such as ClamAV.
We don’t stop here. At Bobcares, security updates and server tuning are an ongoing process. This is because new spam patterns and vulnerabilities can pop up any time in the internet world.
Our 24/7 security experts monitor the mail queue and exim logs regularly to track and filter out new spam patterns in emails, thus ensuring an ongoing 360 degree protection for the mail servers.
See how our 24/7 support team helps you!
2. Anti-spam record lookup
We’ve seen that many spam mails get generated out of email spoofing, where spammers steal valid email addresses and send forged mails with ‘From’ addresses as those IDs, without really authenticating them.
We configure sender and recipient validation in servers to confirm that they are valid domains. Using anti-spam record lookup, we validate that the mails are originated from genuine senders and not spammers who spoof the email addresses.
To prevent email spoofing, the commonly configured anti-spam records are SPF (Sender Policy Framework), DKIM (Domainkeys Identified Mail) and RDNS (Reverse DNS).
While SPF and SKIM are domain authentication records, RDNS is configured to map mail server IP to its hostname. By default, many mail servers do not have SPF checks configured or even if they do, the rule set would be generic.
For instance, a rule that uses ‘+all’ will let mails from every host to pass, which is not useful to block spam. Bobcares’ cPanel experts configure custom ACLs (Access Control Lists) to validate mails and implement filtering to exclude whitelisted domains.
3. Using blacklists in mail server
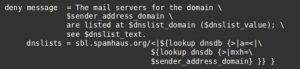
A blacklist, also known as DNSBL or RBL (DNS Blacklist or Realtime Blacklist), is a spam blocking list. SpamCop and SpamHaus are two famous DNS blacklists that contain database of spamming servers.
At Bobcares, we configure ACLs in the customer mail servers to lookup these blacklists and to block spam from those blacklisted servers. To further block abusers, we configure personalized blacklists for each customer server based on the source of the spam coming to them.
[ Take care of your customers, before your competitors do. Get world-class support specialists to support your customers 24/7. ]
4. Blocking IPs
In some worst-case scenarios, where the spamming is out of control and cannot be prevented with spam filters or ACLs alone, we resort to more security measures such as blocking suspicious IPs using firewalls, changing the mail server port, encrypting mails using TLS, etc.
To temporarily defer mails from unknown sources to verify if they are spammers or not, we configure ‘Greylisting’ feature in the cPanel server. This helps us to reduce spam mails without missing out legitimate ones.
Disabling direct access to SMTP ports of mail server, running mail server as an unprivileged user, setting up firewall to monitor SMTP connection traffic, etc. are other security measures we do to prevent cPanel spam.
[ Use your time to build your business. We’ll take care of your customers. Get experienced Hosting Support Specialists at $12.99/hour. ]
How we block outgoing spam in cPanel servers
During our spam investigation process, we’ve noticed that majority of outbound spamming in cPanel servers happen due to email spoofing, where mails are sent using a fake ‘From’ address, which can be a valid email account in the server.
As a result, email bounces or failure messages for these mails would come back to your server’s mail queue and fill it up. Spoofed mails can also lead to your mail server to be blacklisted, which would affect the server reputation and prevent further email delivery.
In our experience fixing outbound spamming in web hosting servers, Bobcares engineers have noticed spoofed mails originating mainly from three sources, which we tackle as follows:
1. Blocking outgoing cPanel spam due to unauthenticated spoofing
Unauthenticated spoofing involves spammers exploiting any vulnerable forms in your server and sending out outgoing spam from it using your local mail server, but with a fake ‘From’ address.
To block outgoing spam from cPanel servers, we configure custom ACL rules in Exim mail server. These rules check the email headers of the outbound mails and get the domain name in the ‘From’ address.
If the domain name in ‘From’ address does not match the domain names in the server, the ACL filter would deny that mail from being delivered using the mail server, thus protecting it from spoofing.
At Bobcares, our Dedicated Support Specialists block outgoing spam in Cpanel servers with their expertise configuring custom ACL rules and ensuring smooth Exim mail server functioning.
[ Don’t lose your sleep over server issues. Keep your customers happy with the best support specialists. ]
2. Block outgoing cPanel spam due to authenticated spoofing
Outgoing spam due to authenticated spoofing happens when the spammers get hold of the details of any email account in your server and use it to send mails with fake ‘From’ addresses.
End user mail accounts can get hacked due to lack of proper care exercised in keeping the login details secure. Viruses or other vulnerability in the user PC or mail clients can also make them vulnerable to hijacks.
While it is not possible for server owners to have control over their customers’ mail devices, our expert support engineers help web hosts protect their servers from these threats and prevent email spoofing and IP blacklisting.
We configure custom ACL rules for the Exim server to check if the authenticated mail user account matches the ‘From’ address of the email that is sent. If there is a mismatch in these addresses, the mail would be rejected.
[ Focus on your core business without interruptions. Our tech support experts are here to manage your customers 24/7. ]
3. Blocking outbound cPanel spam due to server vulnerabilities
Every server software or application has a risk of vulnerability associated with it. Hackers are in the prowl for server vulnerabilities, which can be exploited for their purposes.
Though the default configuration of cPanel keeps Exim as an authenticated relay, adding custom rules or other third party settings may leave open gaps, that allows malicious actors to send out spam.
Bobcares’ cPanel server specialists perform security audits in servers periodically and whenever a change is made in the server settings, to detect any open vulnerabilities and to fix them promptly before an attacker traces it out.
In addition to the protection against email spoofing, to prevent cPanel servers of our customers from sending out outbound spam, we also perform these tweaks:
- Limiting the number of emails each user can send out from the server, after analyzing their requirements.
- Securing the mail server to prevent open relays and restricting access to only valid users.
- Scanning and disabling malicious scripts from sending mails from the servers.
- Configuring anti-spam records such as SPF and DKIM for validating the domains in the server.
- Blocking nobody user from sending out mails using hacked web applications.
- Blocking connections that are not RFC compliant, to block spam mails.
- Setting connection limits per IP to limit the number of mails sent out from malware infected work stations.
- Scanning outgoing messages for spam and virus and weeding out infected mails from going out.
- Configuring reverse DNS for the mail interface IPs to validate the mail server to recipients.
- Subscribing for Sender Feedback Loops to detect and investigate spam complaints promptly.
- Monitoring all Realtime Block Lists for our mail server IPs helps to detect and quarantine the spam source quickly.
- Blocking spam script uploads by implementing upload scanners that work in tandem with anti-virus software.
By increasing the level of logging in exim and monitoring the logs and server load regularly, we are able to review the effectiveness of the security measures we’ve done and to further fine-tune it.
Mail service is perhaps the most important online service that aids day-to-day business transactions. If you’d like to know how you can better support your mail users, we’d be happy to talk to you.



awesome 🙂
ive written this and open source it.
it sort of scan exim mainlog and detect for repeative abuse attack from each user.
thinking to add your advice on relay not matching from: email of the logged in domain
https;//github.com/u007/eximmon