Almost every webmaster starts hosting their website using a shared hosting account. It is a very cost effective method, but sharing resources with other customers can sometimes lead to slow site speed. Over the years, several methods were invented to ensure fair share of resources for everyone in a shared hosting server. One such method is resource usage limitation.
cPanel Support Specialists at Bobcares help online businesses maintain reliable web services. Performance optimization is an important part of our service, and it involves periodic tweaking server settings to avoid resource abuse.
Many server solutions like Apache, MySQL and CloudLinux have ways to limit resource usage of individual accounts in a shared hosting server. One commonly used resource limit is “Number of processes”.
So, how does “Number of processes” cut resource abuse? Let me explain.
Each visit to a website in a shared server is made possible through a “process” in the server. Each process in turn uses up server resources such as Memory, CPU, etc. adding to the server load. So, limiting the number of processes effectively limits the resource usage, and denies one single account a monopoly over server resources.
In CloudLinux servers, “Number of processes” limit is known as “Entry process limit” or “EP limit”. By default, CloudLinux sets this limit as “20”, so that no website can have more than 20 simultaneous visitors at the same time. For an average shared hosting website, this default limit is adequate. When a website tries to open an additional connection over this limit, the error “508 Resource Limit Is Reached” is displayed.
Website abuse is the most common reason for this error to be shown. Situations such as DoS attacks, massive comment spamming and brute-force hack attempts easily exhaust the “Entry Process limit” and show the site as inaccessible. So, it is important to find what is causing the resource limit error before this issue can be resolved.
We help shared hosting providers quickly resolve these errors by systematically tracing the root cause of the issue. Case in point, a support request was recently received at the helpdesk of a shared hosting provider we support. This web host used our cPanel support services to deliver 24/7 technical support. The support request reported that mydomain.com* was showing the error:

“508 Resource Limit Is Reached” as seen by a website visitor
This error meant that mydomain.com was exceeding the “Entry Process limit”. A quick check of the account’s resource allocation showed that “Entry Process limit” was set to 20.
The next step was to find out if the account was indeed using 20 processes. In the CloudLinux terminal, we checked the processes running under mydomain.com:
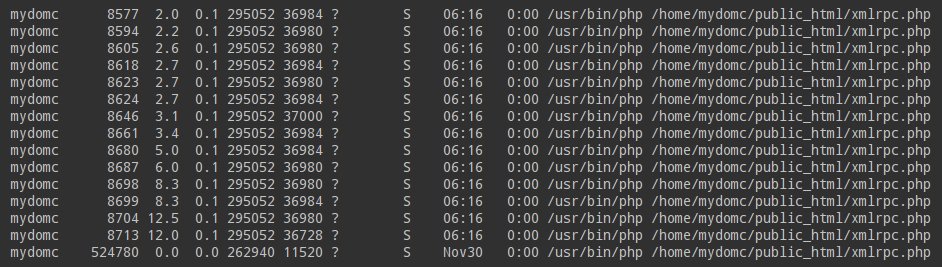
The website mydomain.com reached the Entry Process limit
There were 20 processes running under mydomain.com, which confirmed the resource limit had indeed been exhausted.
The process list also showed something very important – All the processes were requests to access “/home/mydomc/public_html/xmlrpc.php“. “xmlrpc.php” is a file used by WordPress websites to track references of the website in other sites. It looked like another instance of the infamous WordPress xmlrpc pingback attack.
A quick look at the website access logs proved that this was indeed an xmlrpc attack. We then blocked the attacker IPs, and made the file xmlrpc.php inaccessible. This effectively put an end to the attack, and the site came back online.
Other causes for “508 Resource Limit Is Reached process count”
Website abuse is the most common reason for the error “508 Resource Limit Is Reached process count” in CloudLinux servers. Here are some of the common situations we’ve seen, and the resolutions to them:
Comment spamming
When spam bots finds an un-secured web form, massive simultaneous connections are opened to fill the website with spam advertisements. Since such comment spamming is automated, multiple simultaneous connections are opened from different IPs. This exhausts the “Entry Process limit” and renders the website inaccessible.
In such situations, we block the connecting IPs, and activate DNSBL (DNS-based blackhole list) in the web application firewall (such as mod_security). This will prevent any known spammer IP connecting to the server, and rescue the website from further downtime.
Brute force hack attempts
A popular way to hack into a website is to guess the right admin login details. This process is called brute forcing. Attack bots try various combinations of username and passwords at a very high rate from different IPs in order to get admin access. During such attacks, the “Entry Process limit” is easily exhausted.
Such attacks are characterized by a high number of connections to a single file, often lasting for only less than a second. In such cases, we enable DoS protection modules such as mod_evasive, and set the web server to blacklist IPs that show brute force signatures.
Valid increase in traffic
Some websites achieve a sudden increase of valid traffic, usually during a marketing campaign or during festive seasons. In such situations, the solution is to upgrade the “Entry Process limit”. In CloudLinux cPanel/WHM servers, it is modified by going to:
WHM Home >> Server Configuration >> CloudLinux LVE Manager >> Settings >> Edit >> Apply
Summary
Resource limit errors can happen due to a variety of reasons such as brute force attacks, comment spamming and traffic spike. Here we’ve covered a few common causes for such errors in cPanel-CloudLinux servers.
Here at Bobcares our Server Support Engineers help data centers and web hosts minimize service downtimes through 24/7 monitoring, proactive systems audits, 24/7 emergency administration.






Hello,
What command did you use in terminal to display currently running processes?
There is a screenshot above that shows running processes
Hey Jeff,
That’s the output of
topcommand.Hi, It is very helpful can you please tell what is proper command you typed in putty to get the same output as shown in screenshot above
“/home/mydomc/public_html/xmlrpc.php“. “xmlrpc.php”
Where i can donwnload wordpress profiler?