The process of setting up the Linux firewall, iptables, to permit incoming and outgoing network traffic on particular ports used by Docker containers is referred to as “iptables allow Docker port.” At Bobcares, with our Server Management Service, we can handle your issues.
IPtables Allow Docker Port: Introduction
Iptables permit The process of setting up the Linux firewall, iptables, to permit incoming and outgoing network traffic on particular ports used by Docker containers is known as configuring a “Docker port.” In order to allow access from outside systems to the services running inside the containers, Docker containers can expose services that communicate across network ports.
How to allow Docker port traffic through iptables?
1. Recognize the various types of networks that Docker can connect to, including host networks, bridge networks, and user-defined networks. The implications for port exposure and communication vary depending on the type of network. The setting for iptables rules depends on the network mode.
2. Choose the Port for the Container. We must select the port inside the Docker container for which we want to permit traffic. We must also permit access on port 80, for instance, if a web application is operating in a container and exposes port 80.
3. Docker employs Network Address Translation (NAT) to map container ports to host ports whether we’re using the built-in bridge network or a custom one. The actual port we’ll use to access the service from outside the container may be different even though the application within the container listens on a particular port.
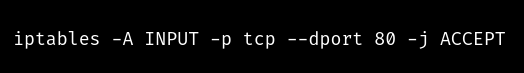
4. We must set up iptables rules in order to permit incoming traffic to a Docker container’s exposed port. The following command allows incoming HTTP port 80 traffic for a container:
5. By default, Iptables rules are not durable, so when the system restarts, they are lost. We can use a program like iptables-persistent to automatically save and load the rules when the machine boots up to make the rules persistent.
6. While allowing traffic via iptables is required for the Docker containers to communicate with the outside world, security must always be taken into account. Make sure we only permit traffic from essential ports and reliable sources. Always adhere to recommended network security procedures.
[Searching solution for a different query? We are just a click away.]
Conclusion
By following the above steps from our Support team, we can easily allow Docker port traffic through iptables.
PREVENT YOUR SERVER FROM CRASHING!
Never again lose customers to poor server speed! Let us help you.
Our server experts will monitor & maintain your server 24/7 so that it remains lightning fast and secure.








0 Comments