Have you ever wonder how to secure sites in IIS?
The effective way to secure a site is by doing IIS hardening.
Here at Bobcares, we have seen several such sever related issues as part of our Server Management Services for web hosts and online service providers.
Today we’ll take a look at the cause for this error and how to fix it.
How to secure sites in IIS
One of the main reasons for site infections or defacing on a Windows VPS Server is poor file security or poor configuration choices when it comes to how IIS should access file content. The effective way to prevent this is to start with a secure site.
How to add the Site to IIS
1. Now let’s look into the process of Secure a Site in IIS via the interface.
1. To add a website in IIS (Internet Information Services), we open up the IIS Manager, right-click on Sites, and select Add Website.
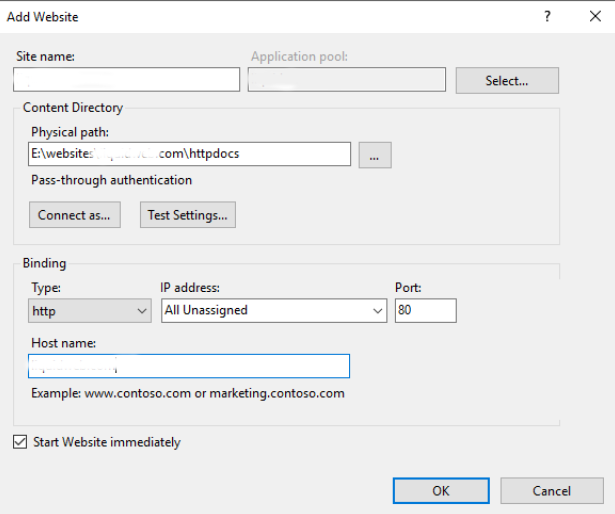
- Site name- Recommend using the domain name as the “Site name” for easy identification.
- Physical path- Provide the path to where the website content is located.
- Configuration options under “Connect as-and “Test Settings do not need to alter*.
2. Next, we set the Anonymous User. To do this, we change the associated Anonymous user and make a few security changes on the website’s content folder.
So, In IIS, we select the new site on the left > in the main window double click on Authentication > Select Anonymous Authentication > Then click the Edit button on the right action bar.
3. In addition, when it comes to hosting multiple domains, we switch IUSR account for sites, and select “Application pool identity” and click OK. Or manually create a user on the system for each site
4. We set Folder Permissions in IIS. Basically, the “ApplicationPoolIdentity” user has very few permissions. So we set up proper security settings for website files.
For that, we browse through your file system and find the folder with the site’s files. Then, we right-click on the folder and go to properties. In the properties interface, select the Security tab. Next, we set up correct security permissions on the folder. Also, we disable inheritance. To do this, we click on Advanced, then click on Disable inheritance.
2. Here, let’s look into the process of Secure a Site in IIS via the interface.
Also, the above steps can be achieved via Powershell, the below steps provided can also be accomplished on a Windows Server 2012 or newer server through Powershell.
1. Initially, we simply fill out the first two variables with the domain name and the path to the content,
2. Then, we run the rest of the PowerShell commands to set up the site in IIS and configure folder permissions.
[String]$Domain = ‘<domain_Name>’ [String]$Root = ‘<path_to_your_content>’ Import-Module WebAdministration
3. Next, we create App pool & Website
New-WebAppPool -Name $Domain New-Website -Name $Domain -HostHeader $Domain -PhysicalPath $Root -ApplicationPool $Domain Set-WebConfigurationProperty -Filter system.webServer/security/authentication/anonymousAuthentication -Location $Domain -PSPath MACHINE/WEBROOT/APPHOST -Name userName -Value ''
4. Optionally add www. Binding
New-WebBinding -Name $Domain -HostHeader www.$Domain -ErrorAction
5. Then, we remove inheritance (copy)
$ACL = Get-ACL $Root $ACL.SetAccessRuleProtection($True,$True) | Out-Null $ACL.Access | ?{ !(($_.IdentityReference -eq 'NT AUTHORITY\SYSTEM') -or ($_.IdentityReference -eq 'BUILTIN\Administrators')) } | %{ $ACL.RemoveAccessRule( $_ ) } | Out-Null $ACL | Set-ACL
6. We add IIS user permissions
$ACL = Get-ACL $Root $acl.SetAccessRuleProtection($False, $True) $Rule = New-Object System.Security.AccessControl.FileSystemAccessRule("IIS AppPool\$Domain", "ReadAndExecute", "ContainerInherit, ObjectInherit", "None", "Allow") $acl.AddAccessRule($Rule) $acl | Set-Acl
That’s it.
[Need any further assistance with server hardening tasks? – We’re available 24*7]
Conclusion
In short, the main reason for site infections or defacing on a Windows VPS Server include poor file security or poor configuration. Today, we saw how our Support Engineers secure sites in IIS.







0 Comments