To run a website, you need several services such as web server, database server, mail server and more.
These services need to communicate with each other to make web apps work.
But in AWS, this communication can break due to default security settings.
Why can’t EC2 instances connect with each other?
AWS servers (aka instances) are configured by default to reject all incoming connections.
Users will have to specifically allow incoming connections to each service port (eg. SMTP port 25, DB port 3306).
For eg. if you want to run a web server, you’ll have to specifically ALLOW “incoming connection” to port 80.
So if your web server needs to connect to a DB server, you’ll need to allow incoming connection from the web server to the DB server’s port 3306.
Connections allowed through “Security Groups”
AWS uses an administration feature called “Security Groups” to allow incoming connections.
It allows you to create common security rules for similar servers.
For eg. Let’s say you have 3 web servers, and need to allow incoming connections to port 80 for all of them. You can create a “Security Group” called “Web Servers”, and create a rule within it to open port 80 to the internet.
Similarly, if you want to allow incoming connection to the database port, you need to
- Create a Security Group for database servers.
- Allow incoming connections to port 3306 from specific IPs or group of servers.
How to connect two ec2 instances – With an example
Here at Bobcares.com, we provide AWS Management & Maintenance services to several web hosts, digital marketers, and other online businesses.
As part of our services, we often setup inter-server connections such as:
- Web to DB server
- Backup servers to all servers
- Web to Mail server
- Monitoring server to all servers
- .. and more
Let’s take an example of a Webserver to Database server connection to show how to connect two ec2 instances.
Step 1 – Find the security group name of both servers
Every instance will have a Security Group assigned by default, which is called, well, “default”.
But the best practice is to always create a custom security group based on the role a server would perform.
This is recommended, because if every kind of server uses the group “default”, rules created for one kind of server (say mail server), will be applied to all. So, web, DB and backup servers will have their SMTP port open to public.
For instance, in some AWS accounts, we’ve created a custom Security Group called “Web Rules” which allows incoming connections to port 80.
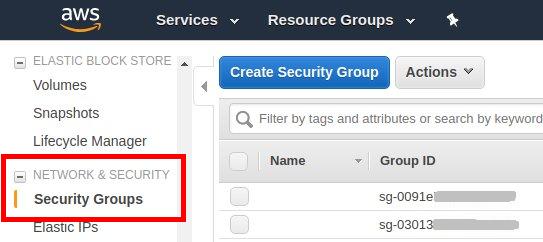
If you already have a running instance, you can find the security group name by going to:
Amazon EC2 console –> Instances –> [ Your Instance Name ] –> Description
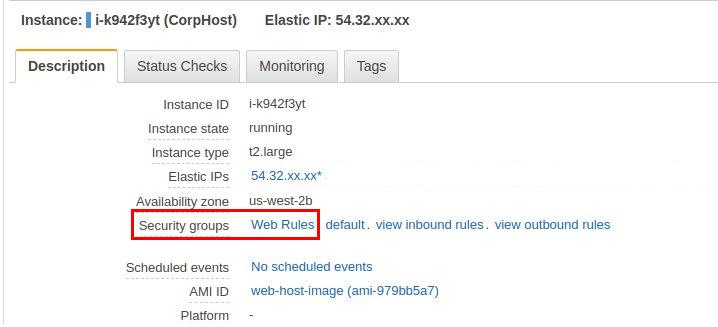
In our example, we have two servers, and one security group each:
- Web server – This server is assigned the security group “Web Rules“, with group ID sg-5cdd840e.
- Database server – This is a MySQL server with the security group name “DB Rules“, with group ID sg-4uioo072k.
Step 2 – Edit recipient server’s security group to allow connections
Now our objective is to allow connections from “Web Rules” security group to port 3306 of “DB Rules” security group.
So, first we edit the DB Rules security group by going to:
Amazon EC2 console –> Security Groups –> DB Rules –> Inbound –> Edit –> Add Rule
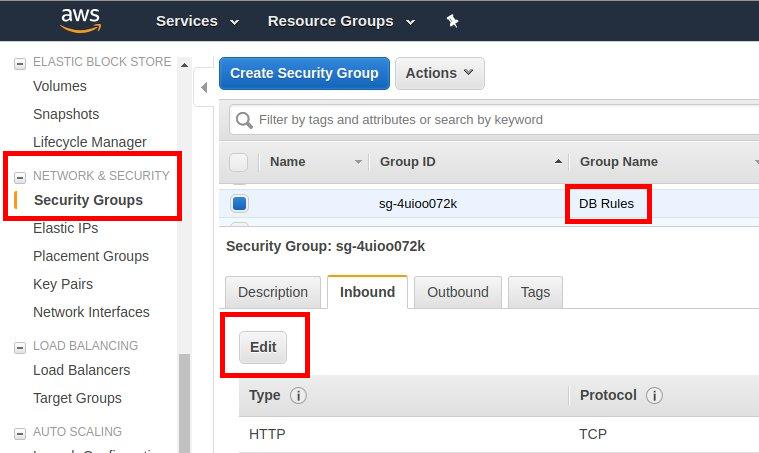
It’ll launch a pop-up window where a custom rule can be added.
In our example, we need to create a rule to allow connections to port 3306 from security group Web Rules
For that, we chose the Type option “Custom TCP Rule” and then the Port as “3306“, and the Source as “Web Rules”.
While typing in the group name, the group ID will be displayed, and we can choose that. In this case, the group ID for Web Rules was sg-5cdd840e.

At this point, ALL servers that are assigned the Security Group “DB Rules” will allow connection to port 3306 from ALL servers that are assigned the group “Web Rules“.
Conclusion
AWS blocks all incoming connections by default. Today we’ve seen how to configure security groups in AWS console to allow connections between two servers.




0 Comments