Configuring Fail2ban to monitor WordPress login is an effective way to prevent brute-force attacks on your website.
Fail2ban constantly monitors the server logs and bans IP addresses that show malicious behavior.
At Bobcares, we use fail2ban as a part of our brute-force attack mitigation steps in our Server Management Services.
To know how we do this, read on.
Security threats in WordPress websites
WordPress is a very popular open-source Content Management System, which makes it equally vulnerable to brute-force attacks.
So, what exactly is a brute-force attack?
It is the simplest method to gain access to a site or a server. Usually, attackers run automated scripts that try thousands of username and password combinations, again and again, until it gets in.
Such attacks often eat up lot of server resources and prevent legitimate users from accessing web and mail services. And in case of these attacks lead to outbound spam, IP blacklisting, and other issues.
If a website is attacked by someone, normally a user would block their IP address in the firewall.
However, it’s quite difficult to do this in a brute-force attack, because the user will have to block a large number of IP address, making this practically impossible.
So the best solution would be to have an automated blocking system for the server, that blocks malicious IP addresses.
This is where Fail2ban comes in. We install Fail2ban and integrate it with WordPress to block login attempts.
How Fail2Ban prevents WordPress brute-force attack?
Fail2Ban is a software framework for intrusion prevention. It monitors log files for events, such as too many login efforts, and create firewall rules to ban the particular IP addresses.
Hence we install it in our servers and add WP fail2ban plugin to the WordPress. Let’s see how to install the WordPress fail2ban plugin.
- Initially login to the WordPress site with admin login and access the Dashboard.
- Next select Plugins from the left panel, this opens a new window.
- Select the Add New option, to add a new plugin.
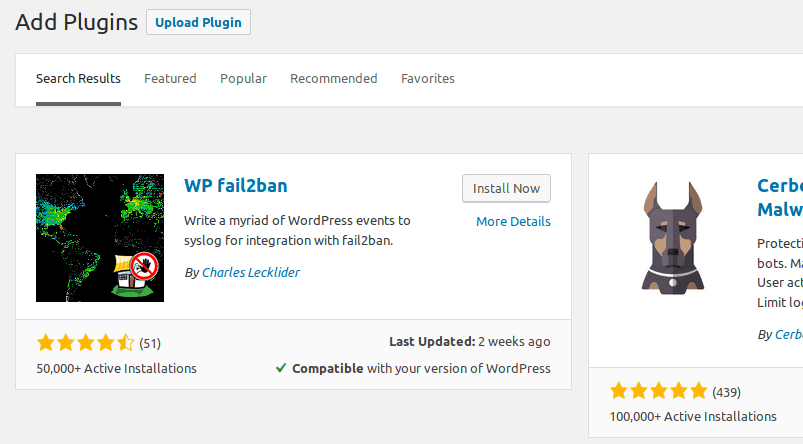
- Search for WP fail2ban in the search bar, which lists the plugin. Click on the Install Now button.
- Later Activate the plugin from the plugin installer.
Once the plugin is installed, we configure fail2ban. Let’s see how we do it.
How to configure Fail2ban to prevent WordPress login attacks?
Basically, here we create rules for blocking IP addresses, that try to login to WordPress with wrong passwords multiple times.
And for doing this we edit the fail2ban local configuration file, that is, /etc/fail2ban/jail.local
[apache-wp-login] enabled = true port = http,https action = iptables[name=WP, port=http, protocol=tcp] filter = apache-wp-login logpath = /var/log/apache2/*error.log maxretry = 3 bantime = 300 ignoreip = <IP that need to whitelist>
Later we save and close this file.
Then we create another file, /etc/fail2ban/filter.d/apache-wp-login.conf. To this file, we add the following,
[Definition] failregex = <HOST>.*] "POST /wp-login.php ignoreregex =
Finally, we save and close this file and restart fail2ban using the command,
systemctl restart fail2ban
Thus the configuration is complete.
[Need assistance in configuring fail2ban? – We are available 24×7.]
Conclusion
In short, to prevent the WordPress brute-force attack, we use fail2ban software which works by continuously monitoring log files and banning IP addresses. Today’s we saw how our Support Engineers configured this.






Thanks, i was looking for this. Im installing it. Hope it works.
Actually fail2ban crashes telling us that host group is missing.
Hi,
Please contact our support through live chat(click on the icon at right-bottom).