Learn how to fix the SSL_ERROR_RX_RECORD_TOO_LONG error code in HAProxy. Our HAProxy Support team is here to help you with your questions and concerns.
An Overview:
How to Fix SL_ERROR_RX_RECORD_TOO_LONG error code in HAProxy
SSL and TLS are cryptographic protocols designed to provide secure communication over a computer network. TLS is the successor to SSL and is more secure and efficient.
These protocols establish a secure channel between two entities, such as a client and a server, ensuring that data transmitted is encrypted and protected from eavesdropping or tampering.
SSL/TLS is essential for maintaining the confidentiality and integrity of data transmitted over the internet, such as sensitive information like login credentials, payment details, and personal data.
By encrypting this data, SSL/TLS helps prevent unauthorized access and data breaches, which are important in today’s digital landscape.
Role of SSL/TLS in HAProxy
HAProxy is a high-performance, open-source load balancer and reverse proxy that facilitates the distribution of incoming traffic across multiple backend servers. SSL/TLS plays a key role in HAProxy by ensuring secure data transmission between clients and the servers it manages.
HAProxy can handle SSL/TLS termination, which means it can decrypt incoming encrypted traffic, process it, and then forward the unencrypted data to backend servers. This offloads the computational burden of encryption and decryption from the backend servers, improving their performance and scalability.
Additionally, SSL/TLS in HAProxy enables secure connections from clients to the load balancer, providing a secure front door to web applications and services.
Common SSL/TLS Errors
SSL/TLS errors can be due to misconfigurations or incompatibilities between clients and servers. Some common SSL/TLS errors that might occur in HAProxy include:
- SSL_ERROR_HANDSHAKE_FAILURE_ALERT:
This error indicates that the SSL/TLS handshake failed due to mismatched protocol versions or cipher suites.
- SSL_ERROR_BAD_CERT_DOMAIN:
This error occurs when the domain name on the SSL certificate does not match the domain name in the URL.
- SSL_ERROR_CERTIFICATE_EXPIRED: This error indicates that the SSL certificate used has expired and needs to be renewed.
- SSL_ERROR_NO_CYPHER_OVERLAP: This error arises when there are no common cipher suites between the client and server.
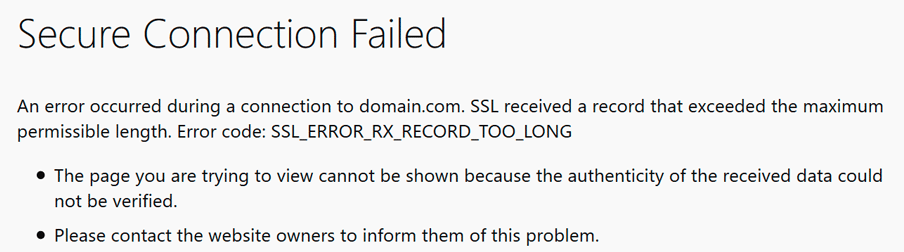
- SSL_ERROR_RX_RECORD_TOO_LONG:
This specific error indicates that the SSL/TLS record received is too long, often due to misconfigurations in protocol versions or ciphers, as discussed in the blog.
Impact of SSL/TLS Errors
SSL/TLS errors can effect application performance and security as seen here:
- SSL/TLS errors can cause disruptions in service availability, leading to downtime and potentially lost revenue for businesses.
- Misconfigured SSL/TLS settings can expose sensitive data to potential attackers, leading to data breaches and compromised user information.
- Frequent SSL/TLS errors can erode user trust in a service, damaging the organization’s reputation and customer relationships.
SSL_ERROR_RX_RECORD_TOO_LONG error
The `SSL_ERROR_RX_RECORD_TOO_LONG` error in HAProxy lets us know that the SSL/TLS record received from the backend server exceeds the maximum permissible length. This can disrupt secure communications and prevent proper data exchange. Let’s explore the common causes and solutions for this error.
Common Causes of SSL_ERROR_RX_RECORD_TOO_LONG
- The backend server may send SSL/TLS records that are too large, which HAProxy cannot handle. This could be due to misconfigured SSL/TLS settings on the backend server, like:
- Incorrect SSL/TLS protocol versions
- Unsupported cipher suites
- Improper key sizes
- Incorrect SSL/TLS record size configuration
- If the SSL/TLS versions or ciphers used between HAProxy and the backend server are incompatible, it can lead to this error. Ensure that the SSL/TLS settings are properly configured on both ends, including:
- Matching SSL/TLS protocol versions
- Supported cipher suites
- Proper key sizes
- The HAProxy configuration may not be set up to handle the SSL/TLS traffic. So, make sure that the SSL/TLS settings, such as bind options, ciphers, and DH parameters, are correctly configured in the HAProxy global and frontend sections. Some common configuration issues include:
- Incorrect SSL/TLS protocol versions
- Unsupported cipher suites
- Improper key sizes
- Incorrect SSL/TLS record size configuration
How to fix SSL_ERROR_RX_RECORD_TOO_LONG error
- To begin with, check the backend server is configured to send SSL/TLS records of the correct size.
- Then, check the SSL/TLS protocol versions and ciphers to ensure they match those supported by HAProxy.
- Additionally, confirm that the protocol versions used by HAProxy and the backend server are compatible.
- Also, make sure that both HAProxy and the backend server support the same cipher suites.
- Furthermore, verify, the HAProxy configuration to ensure SSL/TLS settings are correctly defined in the global and frontend sections.
- Also, verify that bind options are correctly configured to handle SSL/TLS traffic.
- Finally, check if Diffie-Hellman parameters are set up appropriately if needed.
[Need assistance with a different issue? Our team is available 24/7.]
Conclusion
In brief, our Support Experts demonstrated how to fix the SSL_ERROR_RX_RECORD_TOO_LONG error code in HAProxy.







0 Comments