Let’s fix the “Operating system error 5 (Access is denied)” in SQL Server simply with our latest blog. Bobcares, as a part of our SQL Server Support offers solutions to every query that comes our way.
Overview
- Fixing “Operating system error 5 (Access is denied)” in SQL Server
- Impacts of the Error
- Common Causes and Fixes
- Prevention Tips
- Conclusion
Fixing “Operating system error 5 (Access is denied)” in SQL Server
The dreaded “Operating system error 5 (Access is denied)” can disrupt SQL Server operations, leaving administrators scrambling for solutions. This common error occurs when SQL Server lacks sufficient permissions to access or modify a file or directory, often during backup, restore, or file-related operations. Here’s a detailed guide to understanding and resolving this issue.
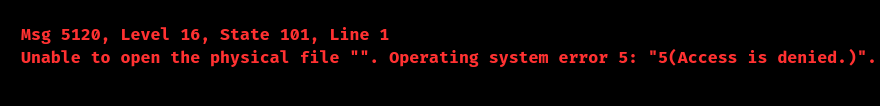
This error signifies that SQL Server’s service account cannot perform the requested operation due to insufficient file system permissions. The typical syntax is as follows:
Impacts of the Error
1. Backup Failures: Database backups are interrupted, posing a risk of data loss.
2. Database Recovery Issues: Some databases may enter a “Recovery Pending” state.
3. Operational Disruptions: Applications relying on SQL Server may fail due to interrupted workflows.
4. Data Loss Risk: Regular backup operations may be compromised, increasing the likelihood of data loss.
Common Causes and Fixes
1. Insufficient Permissions on Backup Directory
Cause: The SQL Server service account lacks permissions to write to the backup directory.
Fix:
Navigate to the backup directory (e.g., C:\Program Files\Microsoft SQL Server\MSSQL\MSSQL\Backup).
Right-click on the folder, select Properties, and go to the Security tab.
Add the SQL Server service account (e.g., NT SERVICE\MSSQLSERVER) and grant Full Control.
Save changes and retry the operation.
2. Service Account Misconfiguration
Cause: SQL Server is running under an account with inadequate permissions.
Fix:
Open SQL Server Configuration Manager.
Navigate to SQL Server Services, right-click the SQL instance, and choose Properties.
Under the Log On tab, change the account to a domain or local account with appropriate permissions.
Restart the SQL Server service.
3. File System Permissions
Cause: The .mdf or .ldf database files lack read/write access for the SQL Server account.
Fix:
Locate the database files.
Right-click on each file, select Properties, and go to the Security tab.
Add the SQL Server service account with read/write permissions.
Save changes and restart SQL Server.
4. Read-Only Attribute
Cause: The target files or directories are marked as Read-Only.
Fix:
Right-click on the file or folder, choose Properties, and uncheck Read-only.
Click Apply, then OK.
5. Network Share Permissions
Cause: The SQL Server service lacks permissions to access a network share used for backups.
Fix:
On the shared folder, navigate to Properties → Sharing → Advanced Sharing.
Click Permissions, add the SQL Server service account, and grant Full Control.
Confirm the settings in the Security tab for NTFS permissions.
6. Group Policy Changes
Cause: A recent Group Policy update restricted access rights for the SQL Server account.
Fix:
Use the Group Policy Management Console (GPMC) to review policies affecting file access.
Roll back or adjust any policies limiting SQL Server’s operational permissions.
7. File Ownership Issues
Cause: Files are owned by a user or group that SQL Server cannot access.
Fix:
Right-click on the file or folder, go to Properties → Security → Advanced.
In the Owner section, click Change, set a new owner (e.g., Administrators), and apply changes.
Prevention Tips
1. Audit Permissions Regularly: Schedule periodic reviews of permissions for SQL Server service accounts.
2. Document Changes: Keep a record of all configuration and policy updates that could impact SQL Server operations.
3. Monitor Logs: Use tools to alert administrators to permission issues before they escalate.
4. Dedicated Service Accounts: Use specific accounts with minimal privileges required for SQL Server operations.
[Searching solution for a different question? We’re available 24/7.]
Conclusion
The “Operating system error 5 (Access is denied)” can be daunting, but understanding its causes and applying these solutions ensures seamless SQL Server operations. By proactively managing permissions and adopting best practices, we can minimize disruptions and secure the database environment.







0 Comments