VMWare vCenter Self-Signed Certificate Warning triggers when we connect to a VMWare vCenter server using a web-browser.
As part of our Server Management Services, we assist our customers with several vCenter server queries.
Today, let us focus on the warning and how our Support Engineers go about with it.
VMWare vCenter Self-Signed Certificate Warning
As we mentioned earlier we face this warning when we connect to a VMWare vCenter server using a web-browser.
In Firefox, we can disable it by adding a vCenter website to the list of exceptions. However, in Internet Explorer the procedure is more complicated.
Default SSL certificates with ESXi and vCenter servers is self-signed. Other systems do not trust them and show a warning or block the connection with these websites.
To disable the warning, we can add the self-signed certificate in the list of trusted certificates. Or we can replace it with our own one issued by a trusted certification authority.
Let us consider the first variant, the procedure is trivial, but there are some not quite obvious moments. Here’s how our Support Engineers go about this.
So, when we open a vCenter server webpage in the browser, a window with the following warning will appear:
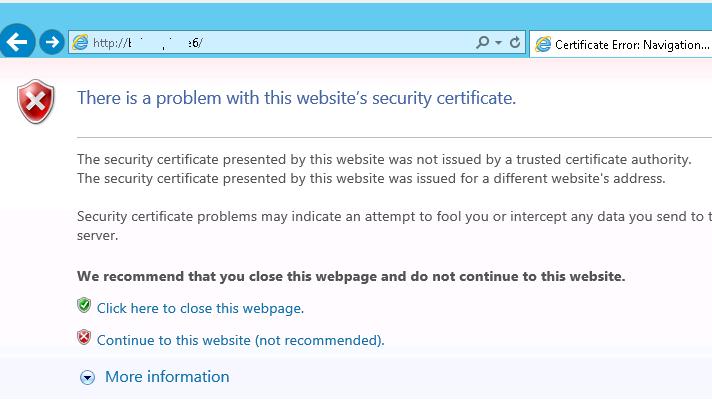
We encounter the warning “The security certificate presented by this website was issued for a different website’s address” since the host name is different from the CN name.
To download the certificate, click Download trusted root CA certificates.
We save the file to any directory. The name of the file is download (with no extension).
Then we change the extension of download to download.zip and extract it with the built-in archiver (Extract All):

The cert archive contains 2 files with the extensions .0 and .r0. Change the file extension .0 to .cer.
Add root CA certificate to trusted certificates:
Now we only have to add this root CA certificate to the list of trusted certificates.
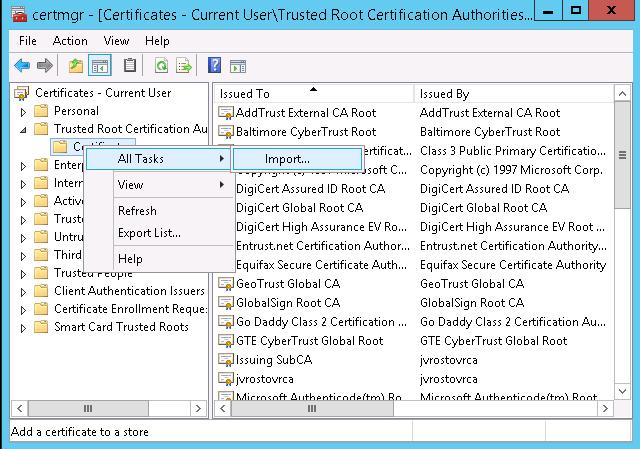
Suppose, we want this certificate to be trusted only with the current account. Open certmgr.msc console, go to Certificates > Trusted Root Certification Authorities and open the certificate import wizard (Import):
We select the certificate file obtained earlier and place it to the Trusted Root Certification Authorities store.
Finally we submit adding the certificate.
A new certificate with the name CA appears in the list:
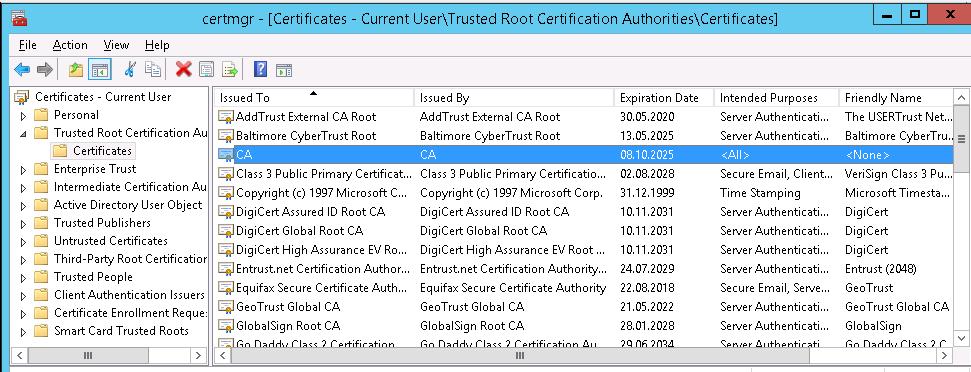
Open the vCenter webpage in the browser again. The warning will not appear.
Generally, these guidelines are applicable to vCenter Server Appliance. If we are using Windows vCenter Server, we can’t download the certificate file. There will be no link to download the archive with the certificate.
This file is on vCenter Server in C:\ProgramData\VMware\SSL\. We have to import the certificate from this directory on a client in the same way.
[Still stuck with the warning? We’d be happy to assist]
Conclusion
In short, removing VMWare vCenter Self-Signed Certificate Warning is a trivial procedure, but there are some not quite obvious moments. Today, we saw one of the easy methods suggested by our Experienced Server Admins.




0 Comments